If you need an SFTP server, you can set it up easily on a Linux box since it’s supported out of the box. But if you’d like to set up one on Windows, you need to do some extra work since SFTP is not natively supported on Windows. Don’t get confused it with the FTPS, short for FTP over SSL, which is supported out of the box with IIS on Windows Servers.
Steps to set up a SFTP/SSH server using OpenSSH on Windows Server 2012 R2
1. Download the latest OpenSSH for Windows binaries. Choose the OpenSSH-Win64.zip package.
2. Extract the package and save them to C:\Program Files\OpenSSH folder.
3. Open an elevated PowerShell console, and run the following commands to install SSHD and ssh-agent services.
cd "\Program Files\OpenSSH" .\install-sshd.ps1
If failed due to the Policy that prevents it from executing, run this instead:
powershell -ExecutionPolicy Bypass -File .\install-sshd.ps1
4. In the same PowerShell console, run the following commands to generate server keys and restrict an access to them.
.\ssh-keygen.exe -A PowerShell -ExecutionPolicy Bypass -File .\FixHostFilePermissions.ps1 -Confirm:$false
5. Open an incoming port in Windows Firewall for the SSH server. You can either run the following PowerShell cmdlet to open it or do it through Windows Firewall set up from Control Panel.
New-NetFirewallRule -Protocol TCP -LocalPort 22 -Direction Inbound -Action Allow -DisplayName SSH
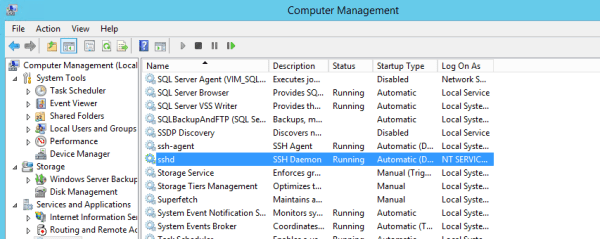
6. Open services window, locate the sshd service and click Start to start the service. If succeed, you are all set. And you need to change the Startup Type to Automatical so the service can be launched automatically.
Testing the connection to the server
You can use any tools that support SSH to connect to the SSH server you just set up, such as FileZilla, WinSCP, PuTTY to name a few. Take WinSCP for example, use the server’s name as Host name, leave the Port number at 22, and type in your Windows user account info as the username and password. If it’s part of the Windows domain, use the format of domain_name\username or username@domain instead.
In some cases where you need to verify the fingerprint of the server, this is how you can find out:
.\ssh-keygen.exe -l -f ssh_host_ed25519_key -E md5
then, when you connect to the SSH server the first time, you can compare the info you just collected with the one popping on the screen.
Alternative options
I had to try a few times to make OpenSSH work for me. But if it doesn’t work out for you, there are a few other options you can try to use as well.
Resources
Installation Guide on WinSCP





There is a typo in 4. Please check. 🙂
Thank you for pointing it out.
Step #4 does not work for me as follows,
PS C:\Program Files\OpenSSH> PowerShell -ExecutionPolicy Bypass -File .\FixHostFilePermissions.ps1 -Confirm:$false
C:\Program Files\OpenSSH\FixHostFilePermissions.ps1 : Cannot convert ‘System.String’ to the type ‘System.Management.Aut
omation.SwitchParameter’ required by parameter ‘Confirm’.
+ CategoryInfo : InvalidArgument: (:) [FixHostFilePermissions.ps1], ParentContainsErrorRecordException
+ FullyQualifiedErrorId : CannotConvertArgument,FixHostFilePermissions.ps1
You can remove $ before “False” or remove -confirm:$false. It will prompt you for each command. I like that way so that you what ps1 script is doing.
>You can remove $ before “False” or remove -confirm:$false. It will prompt you for each command. I like that way so that you what ps1 script is doing.
Thanks for the tip!
Win32-OpenSSH has an issue about this so will follow that one:
https://github.com/PowerShell/Win32-OpenSSH/issues/844
I could do steps 1-6 all were successful.
Could not connect to the server – Software caused connection abort
Step 6 causes a problem for me. I can’t locate sshd in the list, because it’s not there. Step 1-5 could (eventually) be executed successfully. Any ideas?
I’ve run into the same issue :/
After looking around a bit more, it shows up as OpenSSH SSH Server instead of just sshd.
After poking around a bit more, it showe up as OpenSSH SSH Server instead of just sshd with v7.7.2.0p1-Beta, released in July.
Screenshot of services.msc: https://i.imgur.com/hnSsGNj.png
I got this error, when trying to run ssh-keygen.exe -A
Could you help me to have a look?
PS C:\Program Files\OpenSSH-Win64> .\ssh-keygen.exe -A
ssh-keygen: generating new host keys: RSA Could not save your public key in __PROGRAMDATA__\\ssh/ssh_host_rsa_key.SUifL1
g3Uy: No such file or directory
ssh-keygen: generating new host keys: DSA Could not save your public key in __PROGRAMDATA__\\ssh/ssh_host_dsa_key.cacr5a
Vk02: No such file or directory
ssh-keygen: generating new host keys: ECDSA Could not save your public key in __PROGRAMDATA__\\ssh/ssh_host_ecdsa_key.0C
Tq6ro3Av: No such file or directory
ssh-keygen: generating new host keys: ED25519 Could not save your public key in __PROGRAMDATA__\\ssh/ssh_host_ed25519_ke
y.pKnj1ynArI: No such file or directory
I manually copied the files to C\ProgramData\ssh. It’s a hidden folder. I also found that I had to run everything from C:\Program Files\OpenSSH
Step 4 has failed for me as well: .\ssh-keygen.exe -A
After manually creating the C\ProgramData\ssh it started working. Great instructions – thanks.
Thanks for the simple guide.
But how about using keys instead of username/password? A simple tutorial on this would be great!
Unfortunately there’s not much on the internet about OpenSSH on Windows 2012.
Thank you for writing this guide, was really useful and accurate to setup my first SSH server on a Windows Server 2012 environment. I was wondering if someone here can help me out with two issues :
1) change the home root folder of the SSH Server > the first thing a SFTP client shows when connecting is the c:\users\”username logued in folder”. What if I want to set up a different home folder?
2) Is there any way to setup specific user permissions on which folders to edit/view like an ordinary ftp server?
Thank you guys!
I can’t find the SSH service after performing all steps.
Am I doing something wrong?
Thanks!
Has encontrado solución para tu consulta del punto 1, tengo el mismo problema y no encuentro como, he modificado 1000 veces el fichero ssh_config sin exito.
DId you get any info on this, looking to setup user accounts and have isolated folders for each user….
Thanks!
Did you get solution for your problem that is setup user accounts and have isolated folders for each user?
I can’t change the foldername for the chroot of the sftp server. Modifications in the sshd_config files are not accepted, like authentication methods (password and or key autnentication). Not even after complete reboot.
Since the modifications in the [install_location\]sshd_config file are not applied, it looks to me Windows is not even reading this config file, so it is not yet linux compatible. I hope somebody can show me the way of how to set these in sftp via open-ssh in Windows 2012 server.
Friends,
I installed OpenSSH on a server that is in the xxx.gov.br domain. However, when I try to log in through an account (administrator) of that domain, Putty crashes and presents the following message:
“Network error: Software Caused connection abort”
Could someone please help me with this?
Is it possible to integrate the AD to SFTP?
what a freaking waste of time…..this does not work in windows server 2016….it fails when generating the rsa keys. I’ve tested so many windows ssh solutions over the years and none of them worked! If you want ssh get ubuntu….there’s no such thing as ssh in windows…..
Thank you indeed for very nice guide.
Very minor deviatin in step 6 the services are shown as OpenSSH SSH Server and not sshd.
Thank you again for very vlear step by step description.
The end of the article includes a list of several alternatives to Open SSH. Another alternative might be https://www.rebex.net/tiny-sftp-server/. Rebex Tiny SFTP Server – a free, minimalistic SFTP server for Windows. It doesn’t need to be installed. You just unzip the package and run it. Well, optionally you can edit the text config file, but for testing purposes, it’s usually sufficient as it is. Disclaimer: I’m one of the developers behind it.